
A10 Networks Products
Hula Is Your Source For A10 Products
Hula Networks is an authorized A10 Networks reseller with the experience and expertise to provide customers with the right equipment solutions for the best price.
Buy New A10 Networks
Use our form to request A10 Networks product pricing or information on any A10 product.
If you require immediate information regarding used A10 equipment, you can call 1.866.HULANET or during our office hours (between 8AM and 5PM Pacifc) for the latest A10 product inventory.
Hula Has The A10 Equipment You Are Looking For...Or We Can Get It!
As a premier A10 reseller, Hula Networks has direct factory direct access to A10 Networking equipment. If you need A10, Hula can supply the equipment you need with pricing that fits your budget.
About A10
A10's vision is to protect customers with best-in-class solutions and services needed to win the cyberwar.
Who is A10? A10 Networks is more than a technology company. A10 provides security, intelligence and automation across their entire portfolio of secure application solutions services. A10's mission is clear: To enable intelligent automation with deep machine learning to ensure business critical applications are protected, reliable and always available.
A10 Products
Thunder® ADC
LOAD BALANCING & APPLICATION DELIVERY
A10 Thunder® ADC (Application Delivery Controllers) are high-performance solutions to enable customer applications to be highly available, accelerated and secure.
Features & Benefits Include:

ADVANCED SERVERLOAD BALANCING
Complete full-proxy L4-7 load balancing with customizable server health checks and aFleX® L7 scripting.GLOBAL SERVER LOAD BALANCING (GSLB)
Extend load balancing on a global basis to enable worldwide business continuity with faster, localized server responsesAPPLICATION DELIVERY PARTITIONS (ADP)
1,000-plus partitions offer the highest-density, multi-tenant solutions for customizable policies and appliance consolidation.SSL OFFLOAD WITH PFS AND ECC
Perfect Forward Secrecy with a full cipher suite, including Elliptic Curve, provide SSL offload at the industry's highest levels.APPLICATION ACCELERATION AND OPTIMIZATION
Caching, compression and TCP reuse combine to expedite content transfer for enhanced app performance.WEB AND DNS PROTECTION
Secure services and meet compliance targets better with single sign-on, web and DNS firewalls, and DDoS protection.PER-APPLICATION ANALYTICS
Integrate with the A10 Harmony™ Controller for visibility into user experiences, traffic profiles and health checks to improve performance.AXAPI® REST-BASED PROGRAMMABILITY
Configure all features with 100 percent API coverage and enable third-party management.
Lightning™ ADC
CLOUD-NATIVE APP DELIVERY & SECURITY
A10 Lighting™ ADC (Application Delivery Controller) provides application load balancing and traffic management, security and per-app analytics for workloads in public, private or hybrid clouds.
Features & Benefits Include:

APPLICATION LOAD BALANCING
Increase app availability and performance with advanced load balancing, content-based routing, session persistence and granular policy enforcement.ELASTIC SCALING
Use elastic load-balancing and optimized traffic-engineering to manage variable application traffic and optimize scale, performance and availability.APP SECURITY & MALWARE PROTECTION
Defend apps against cyber attacks with web application firewalls, DDoS mitigation, malware protection and other application security capabilities.PER-APPLICATION ANALYTICS
Identify application trends and issues, streamline troubleshooting and effectively meet capacity requirements to deliver superior user experiences.OPTIMIZE AND ACCELERATE TRAFFIC
Improve application response times by utilizing compression, caching, connection multiplexing, SSL offload and other capabilities.ENHANCE CI/CD
Programmatically steer traffic to new deployments, integrate with CI/CD tool chains and gain side-by-side analytics for blue and green deployments.INCREASE DEVOPS AGILITY
Improve automation and self-service with 100 percent API-driven infrastructure, and integrate with container orchestration systems and multi-cloud app deployments.CENTRALIZED CLOUD MANAGEMENT
Choose between a SaaS-based or self-managed A10 Harmony™ Controller for centralized management and analytics across data centers and clouds.
A10 Thunder TPS
DDOS Detection & MITIGATION
The world's highest-performance DDoS protection solution, the A10 Thunder TPS™ (Threat Protection System) detects and mitigates megabit to terabit DDoS attacks at the network edge. A10 Thunder TPS™ offers fast, precise and scalable DDoS attack detection and mitigation.
Features & Benefits Include:

SURGICAL MULTI-VECTOR DDOS PROTECTION
Mitigate volumetric, protocol, resource, application and IoT-based DDoS attacks while protecting legitimate users.POWERFUL & EFFICIENT
Lower TCO with industry-best 300 Gbps at 440 Mpps. FPGA-based acceleration mitigates without burdening CPUs.AUTOMATED THREAT MITIGATION
Respond faster and minimize manual changes with automated mitigation and escalation based on 28 behavioral indicators.PRECISE DETECTION
Swiftly detect attacks with in-line or flow-based methods, or integrate third party detection with open APIs.HYBRID DDOS PROTECTION
Thunder TPS on-premise protection works in concert with the DDoS Protection Cloud service, to provide full spectrum protection. The service is backed by global points of presence and orchestrated by A10 DSIRT.FLEXIBLE MANAGEMENT
Use 100 percent API coverage for SecOps, on-box GUI, CLI, or to manage multiple TPS devices via aGalaxy.THREAT INTELLIGENCE SERVICE
Leverage more than three dozen intelligence sources to block malicious traffic. Included with A10 support.24-7 Attack Support
Spin up 24-7 DDoS attack support from the A10 DDoS Security Incident Response Team (DSIRT). Included with A10 support.
A10 Thunder SSLi
SSL VISIBILITY & DECRYPTION
The most comprehensive decryption solution, A10 Thunder® SSLi® (SSL Insight) decrypts traffic, enabling security devices to analyze all enterprise traffic without compromising performance.
Features & Benefits Include:

DECRYPT ACROSS PORTS AND PROTOCOLS
Decrypt traffic across all standard TCP ports and advanced protocols like SSH, STARTTLS, XMPP, SMTP and POP3.FULL-PROXY ARCHITECTURE
As a full proxy, ciphers can be re-negotiated to ciphers of similar strength to prepare for future ciphers or TLS versions.ICAP-COMPATIBLE
Acting as an ICAP client, Thunder SSLi passes traffic to a network's existing DLP systems without the need for extra solutions.FIPS 140-2 LEVEL 3 COMPLIANCE
The only SSL decryption solution that supports up to four internal HSMs, and multiple external HSMs, to secure private keys.URL BYPASSING
Selectively bypass traffic decryption to enforce privacy policies using a list of over 460 million domains.URL FILTERING
Categorizes over 460 million domains to maximize employee productivity and security by blocking malicious websites as well as to selectively bypass decryption for compliance.LOAD BALANCING AND STEERING
Increase security capacity by load-balancing multiple security devices and selective traffic steering based on fine-grained policies.APPCENTRIC TEMPLATES
Reduce deployment times, and simplify configuration, management and troubleshooting with the AppCentric Templates.
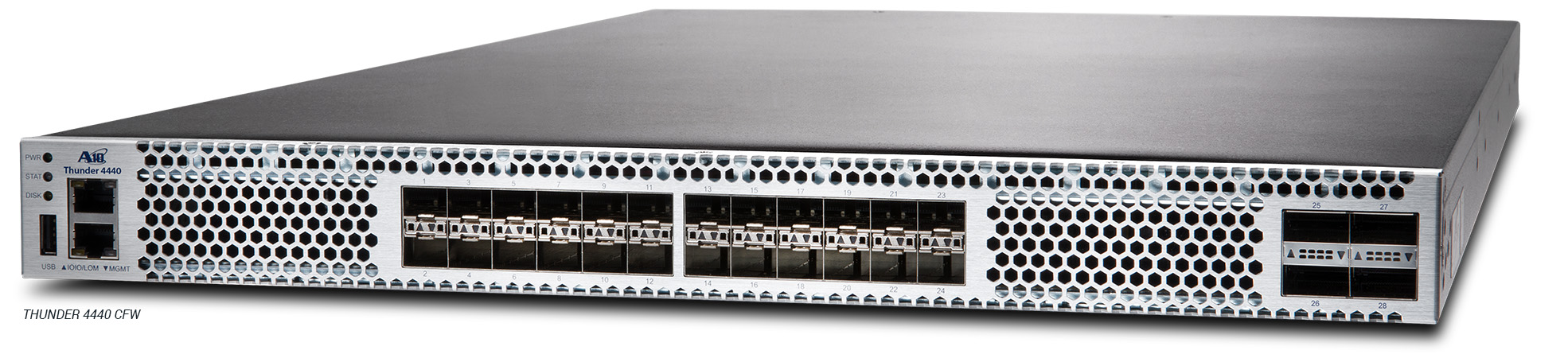
A10 Thunder CFW
CONVERGED FIREWALL, VPN & SECURE WEB GATEWAY
A10 Thunder® CFW (Convergent Firewall) consolidates data center firewall, Gi/SGi firewall, secure web gateway and IPsec site-to-site VPN capabilities into a single solution that also includes all Thunder ADC, CGN and SSLi features.
Features & Benefits Include:
HIGH-PERFORMANCE STATEFUL FIREWALL
Delivers up to 220 Gbps of throughput and supports up to 256 million concurrent sessions in a one rack-unit (RU) appliance.EFFECTIVE POLICY ENFORCEMENT
Up to 128,000 firewall rules enable granular and flexible policies to filter and monitor incoming connections and traffic.INTEGRATED SITE-TO-SITE VPN
Encrypt communication between data centers with IPsec VPN to ensure data privacy and security.BUILT-IN DDOS PROTECTION
FPGA-based Flexible Traffic Acceleration (FTA) mitigates common anomaly attacks before burdening CPUs for DCFW functionality.ADVANCED SERVER LOAD BALANCING
Reduce footptrint and CAPEX/OPEX by combining DCFW with application delivery, NAT and IPsec features in a single appliance.FLEXIBLE DEPLOYMENT OPTIONS
Support traditional north-south and east-west traffic for both IPv4 and IPv6 networks with high-availability (HA) mode.LOGGING AND COMPLIANCE
High-speed logging for all session activities in CEF format and per-rule statistics for SIEM integration.HIGH-SCALE MULTI-TENANCY
Define unique policies by service, application or tenant to efficiently scale data center security.
A10 Thunder CGN
CGNAT & IPV6 MIGRATION
A10 Thunder® CGN (Carrier-Grade Networking) is an award-winning, high-performance IPv4 preservation and IPv6 migration solution.
Features & Benefits Include:

ADVANCED CGNAT
CGNAT scales networks to overcome IPv4 exhaustion with NAT44(4) and ALGs to support network growth and seamless user experiences.IPV6 MIGRATION
Manage the IPv6 transition lifecycle with translation and tunneling protocols, such as NAT64/DNS64, DS-Lite, Lw4o6, 6rd and MAP-T.INTEGRATED DDOS PROTECTION
Defend NAT IP address pools from targeted DDoS attacks for maximum service uptime.APPLICATION LAYER GATEWAY
Operate applications transparently with ALG support, including FTP, TFTP, RSTP, PPTP, SIP, ICMP, MGCP, DNS, H.323 and ESP.ADVANCED LOGGING FEATURES
Comprehensive, high-speed logging options help meet stringent compliance requirements.STATEFUL SYNCHRONIZATION
Hitless failover ensures an uninterrupted user experience by maintaining session state.SCALE & PERFORMANCE
Up to 300 Gbps of throughput and 512 million concurrent sessions in a single appliance.READY FOR SDN & NFV
On-demand software options with virtual or bare metal form factors, and integrates with OpenStack, SDN fabrics and NFV MANO.
A10 AGALAXY®
CENTRALIZED MANAGEMENT SYSTEM
Optimize global monitoring, consolidate management tasks and simplify operations for large-scale Thunder® ADC and Thunder TPS® deployments.
Features & Benefits Include:

UNIFIED POLICY MANAGEMENT AND REPORTING
Consolidate all management and reporting tasks in one location and easily apply consistent policies across all devices.NETWORK TROUBLESHOOTING
Identify, diagnose and resolve problems, including application performance and DDoS-based challenges, before they impact user experiences.ON-DEMAND DDOS MITIGATION CONSOLE
Apply DDoS mitigation templates or custom countermeasures to surgically block suspicious activity.DEVICE MANAGEMENT
Centrally manage devices, SSL keys and certificates, configurations, aFleX® scripts and operations for backups, upgrades and restoration.REAL-TIME DASHBOARD
Gain detailed device information, event data and audit logs for network availability, usage, performance, inventory, history and logins.ADVANCED ACCESS CONTROL
Deploy role-based access control management and external authentication policies that support RADIUS and TACACS+.aXAPI® REST-BASED PROGRAMMABILITY
JSON-based REST API programmatically controls ADC and TPS functionality from other orchestration controllers and cloud management platforms.THIRD-PARTY INTEGRATION
Integrate with third-party DDoS detection systems to automatically recognize DDoS attack protocol anomalies, traffic surges and bot requests.
